Introduction
This document provides an overview of the LiveVox password management functionality. It also includes general guidelines for the client level SFTP credentials.
Password Management features
General Guidelines
Below are the general guidelines for LiveVox portal and agent portal access:
- Username and password are case sensitive.
- Restrictions on the password are as below.
- Password strength is selectable at three levels:
- Medium: User and agent passwords must be a minimum of eight characters in length containing at least one digit and one letter. The password should not match the previous four passwords for that user or agent credential.
- Strong: User and agent passwords must be a minimum of eight characters in length containing at least one digit, one letter, and one special character. The password should not match the previous four passwords for that user or agent credential.
Very Strong: User and agent passwords must be a minimum of twelve characters in length containing at least one digit, one letter, and one special character. The password should not match the previous four passwords for that user or agent credential.
Special characters supported are the ASCII printable characters and they are: (space) ! " # $ % & ' ( ) * + , - . / : ; < = > ? @ [ \ ] ^ _ ` { | } ~
Permitted voice portal users can set the account password temporarily and force the users or agents to change the password on the first login or when the password is updated. If permitted voice portal users change the password for their own user account, they are not prompted to change the password. This feature is configurable at the client level and applied to both users and agents.
User and agent passwords expire after a specified period. The timeframe is configurable at the client level, is set to 90 days by default, and applied to both users and agents.
The system locks out users and agents after a number of failed login attempts. The allowed number of failed logins is configurable at the client level for users and agents. By default, both users and agents are allowed 5 failed logins. This is configurable at the client level.
Passwords are encrypted for all users, meaning that passwords are not stored in clear text anywhere in the system including the database. LiveVox uses AES-256 encryption.
- Password strength is selectable at three levels:
- SFTP site access - Users can upload campaign files or retrieve generated reports from their LiveVox SFTP site. LiveVox uses the SFTP protocol by default. If you require FTP instead, please contact Client Services - client-services@livevox.com.
- If utilizing the voice portal's integrated FTP Browser, a user's voice portal credentials are used (password requirements described above).
- If utilizing a 3rd party SFTP browser application, specific SFTP credentials provided by LiveVox are used. These credentials adhere to the following standards:
- SFTP usernames and passwords are case sensitive.
- SFTP passwords must be a minimum of eight characters in length and contain at least 1 digit.
- SFTP passwords do not expire.
- SFTP encrypts commands and data both, preventing passwords and sensitive information from being transmitted in the clear over a network.
Security Settings
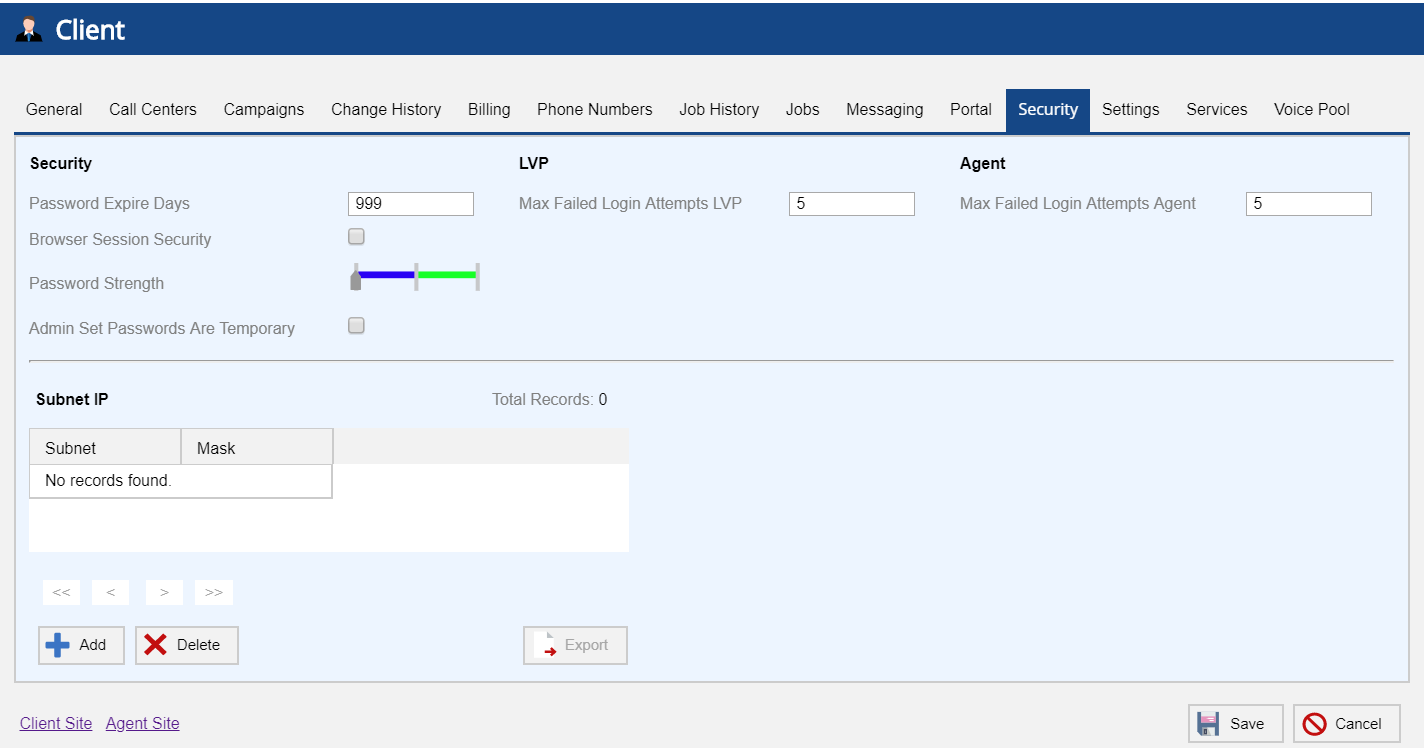
Users in the Sysadmin role can manage LiveVox Voice portal users and agents password security settings through the Security tab of the Client editor.
Client editor - Security Tab
Sysadmins have the option to configure the following options for LiveVox Voice portal users and agents:
Password Expire Days - Allows to set number of days for the password expiration. Applies to both users and agents.
When implementing a password expire period for the first time or reducing the number of days in the current period, it is recommended that all agents be logged out to prevent any call interruption due to password expiration. In addition, if your portal uses any LiveVox Custom Applications (Scripter, for example) or you are unsure if you have integrated these types of apps, please reach out to your Account Management team before adding, removing or making any changes to the Password Expire Period as this may interrupt any active LiveVox Custom Applications.
- Max Failed Login Attempts - Allows to set number of password attempts after which the user or agent gets locked out. The value of Max Failed Login Attempts LVP and Max Failed Login Attempts Agent must be between 1 and 9. Zero, null, and characters are invalid.
- Browser Session Security - If selected, users have to log back in any time the browser is closed.
Password Strength - Slide the arrow on the bar to select one of the following levels:
Medium - Password must be a minimum of eight characters in length containing at least one digit and one letter. The password should not match the previous four passwords.
Strong - Password must be a minimum of eight characters in length containing at least one digit, one letter, and one special character. The password should not match the previous four passwords.
Very Strong - Password must be a minimum of 12 characters in length containing at least one digit, one letter, and one special character. The password should not match the previous four passwords.
Admin Set Passwords Are Temporary - If selected, the system forces the users or agents to change the password on the first login or when the password is updated. Once they login with the temporary password, they are asked to change the password.
Setting up Agents and Users
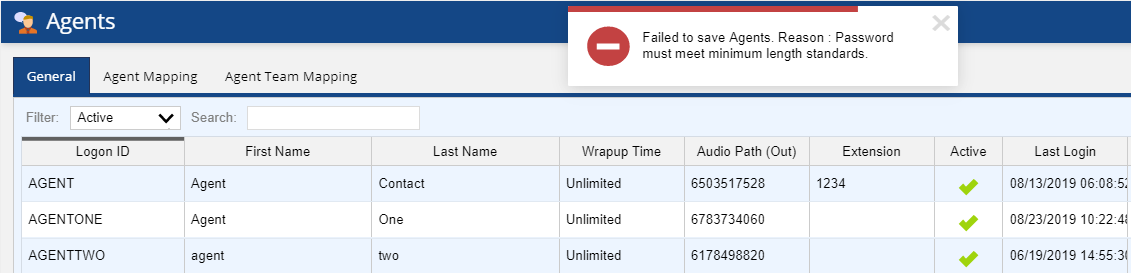
- Adding a new agent - If the password does not contian the required number of characters or greater, does not contain a mixture of characters and numbers, or matches one of the previous four passwords, the user configuring the agent gets the following errors, after clicking the Save.
- If the password has less than the required number of characters, the user configuring the agent gets the following error:
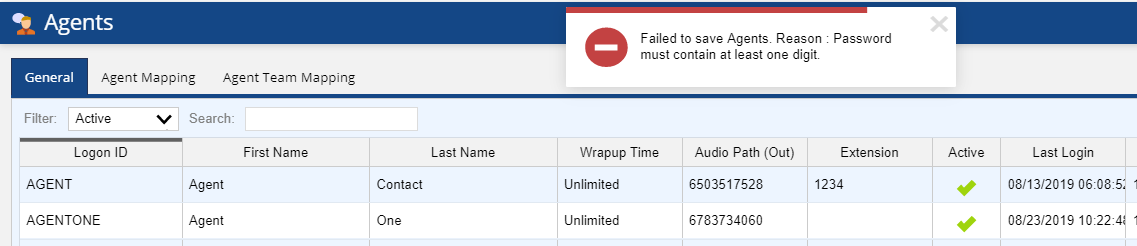
Failure to save agent - If the password has no digits but characters only, the user configuring the agent gets the following error:
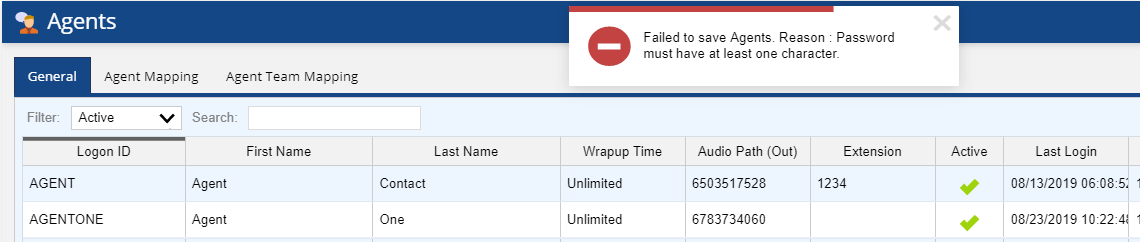
Failure to save agent - If the password has no characters but digits only, the user configuring the agent gets the following error:
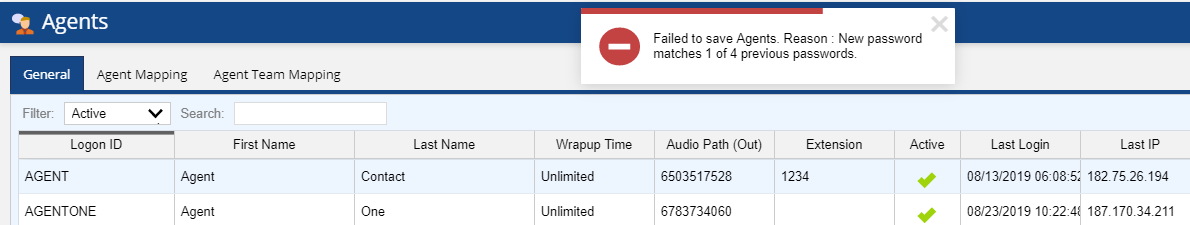
Failure to save agent - If the new password matches with one of the previous four password, the user configuring the agent gets the following error:
Failure to save agent
- If the password has less than the required number of characters, the user configuring the agent gets the following error:
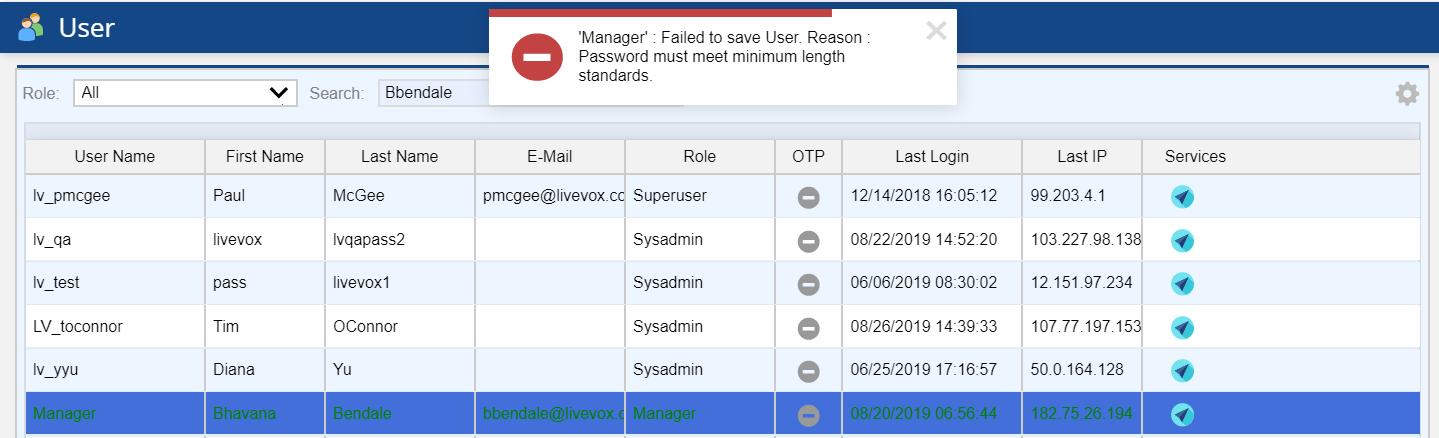
- Adding a new user - Similar as Agent password errors, if the user password does not contain the required number of characters or greater, does not contain a mixture of characters and numbers, or matches one of the previous four passwords, the user configuring the agent gets the error, after clicking the Save.
The below screenshot shows the example of the password with the required number of characters. The user configuring the agent gets the following error:
Failure to save new User
Logging In
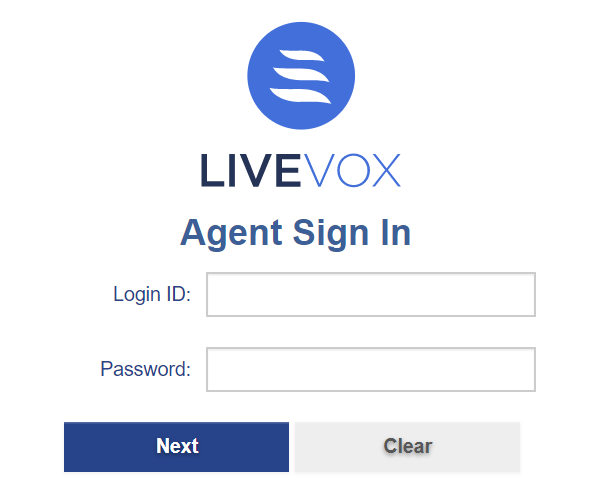
Agent Login
Agents can log in through the agent link provided by LiveVox. Enter Login ID and Password. Click the Next button to log in.
Agent Login
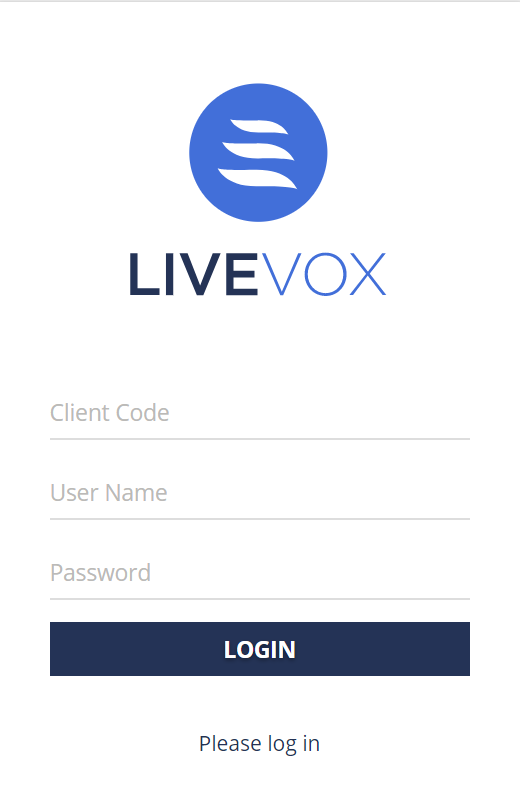
User login
Users can log in through the user link provided by LiveVox. Enter Client Code, User Name, and Password. Click the Login button to log in.
User Login
For more information on failed login, see Failed Logins section.
If the account password is set temporarily, then the system forces the users or agents to change the password on the first login or when the password is updated. Once they login with the temporary password, they will be asked to change the password. For changing the password, see Resetting Expired Password section. If the Dual Factor Authentication (DFA) functionality is enabled, see Changing Passwords section for more information.
Resetting Expired Password
When the password expires, agents and users get an error on their screen as they try to log in. New password cannot be the same as the last four passwords.
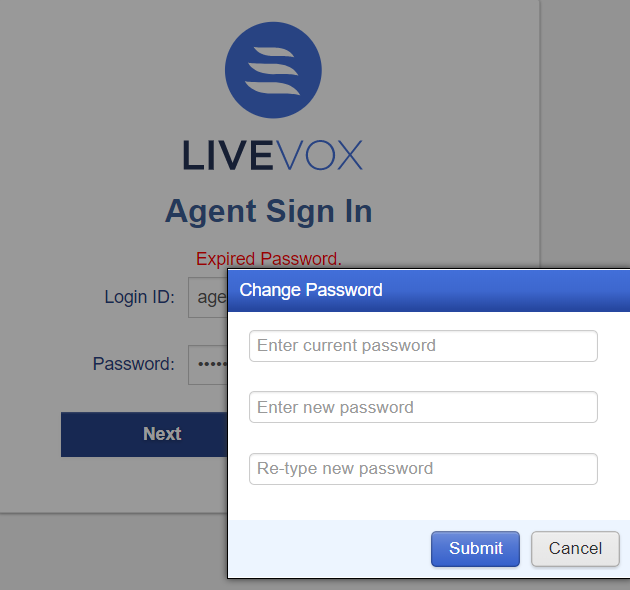
- Agents
Agent sign in for expired password - Users
User password expired
Failed Logins
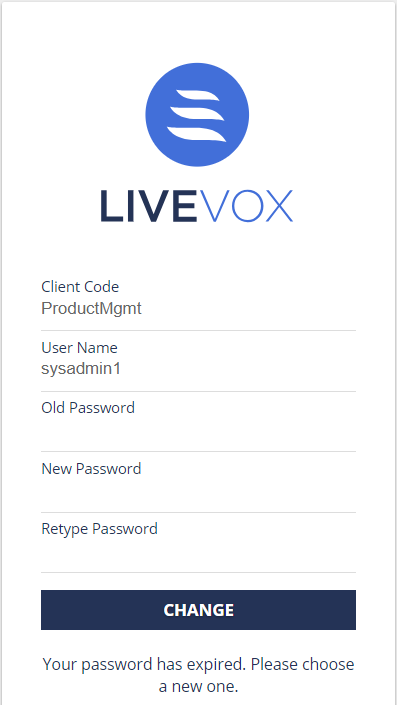
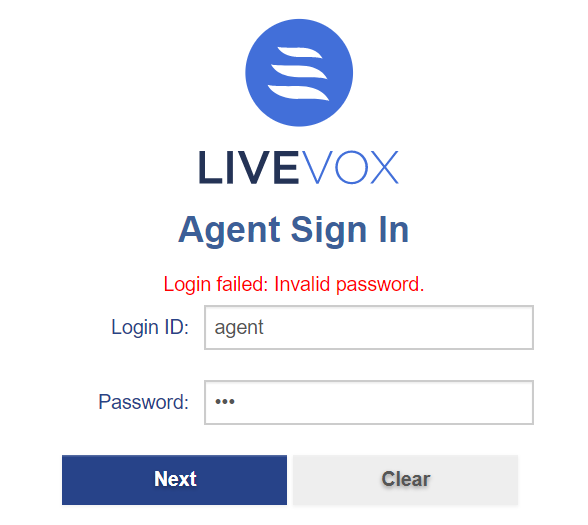
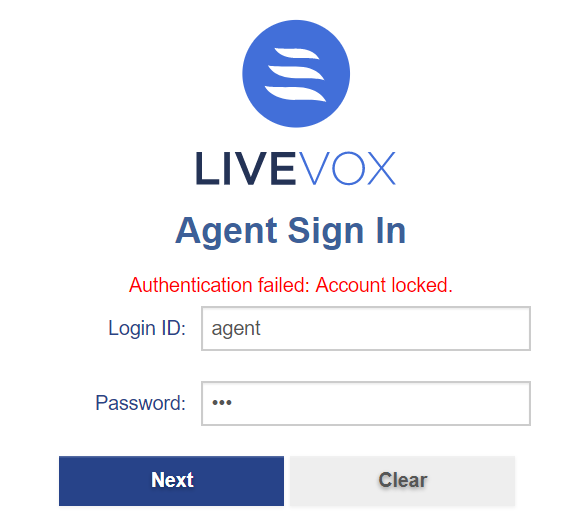
- Agents :
- The Agent login screen displays error message when an invalid password is entered by an agent.
Agent login failed - If an agent attempts to log in with the wrong password more times than the site’s configured limit, the agent is locked out and presented with the following screen:
Agent account locked
- The Agent login screen displays error message when an invalid password is entered by an agent.
- Users
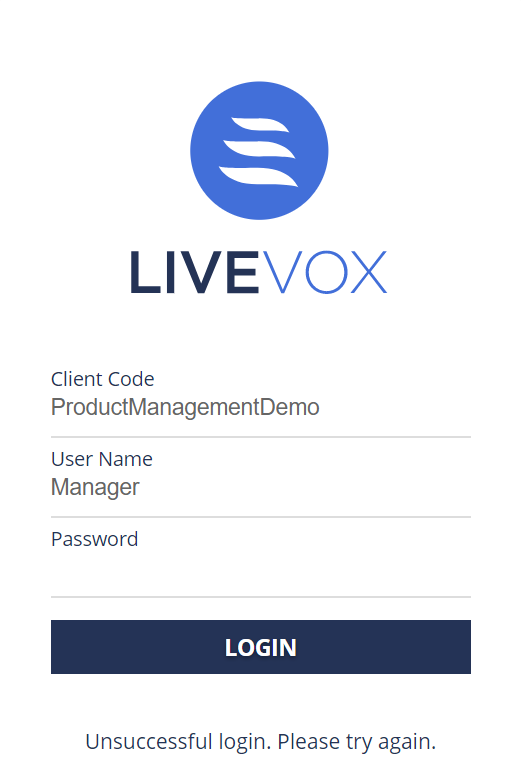
- The login screen displays the following message when an invalid password is entered by the user.
Unsuccessful User login - If a user attempts to log in with the wrong password more times than the site’s configured limit, the user will be locked out and presented with the following screen:
User account locked
- The login screen displays the following message when an invalid password is entered by the user.
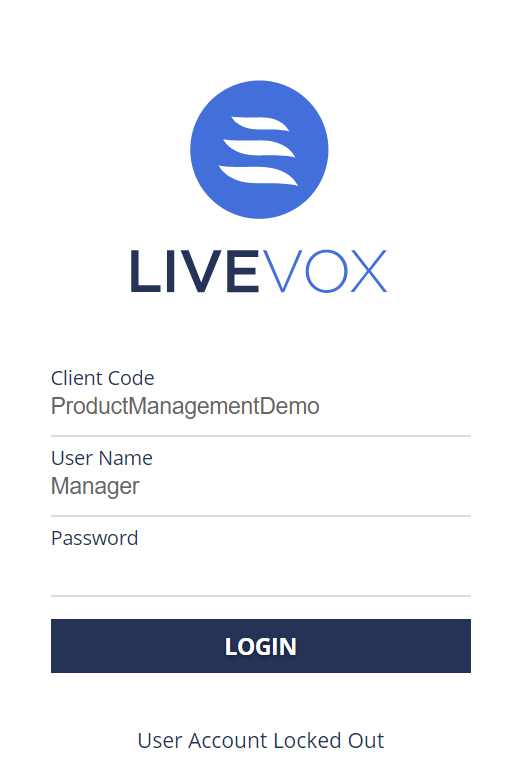
- To unlock the user or agent, permitted user can double click on the lock icon and confirm the action from User or Agents editor.
Example of unlocking the locked agent
Dual Factor Authentication
Dual Factor Authentication (DFA) is a type of Multi Factor Authentication, where essentially second level of authentication by user is required for a successful login, and this second password is an OTP (One Time Password).
- Please contact LiveVox Client Services to enable Dual Factor Authentication option and specify Max Failed Login OTP Attempts.
- Dual Factor Authentication is not available for agent login.
- Second-factor authorization is not supported via email, SMS and voice message.
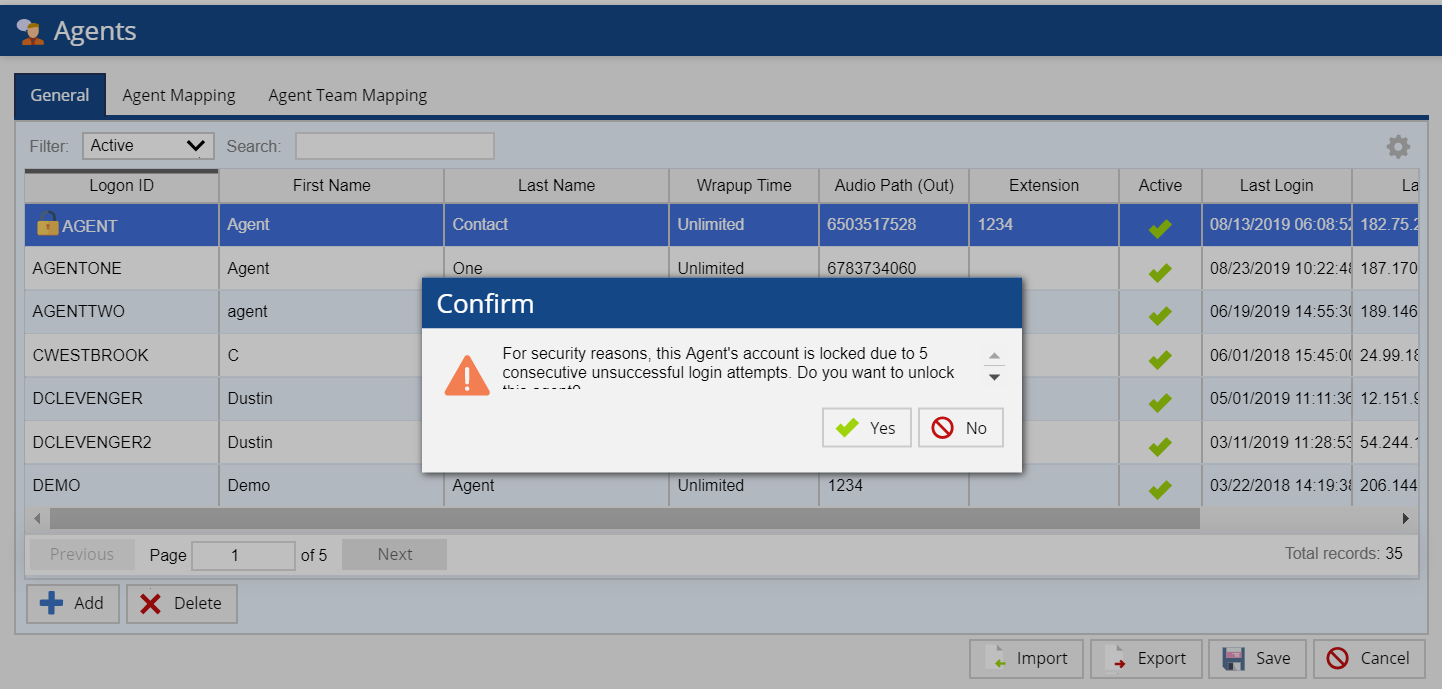
An Admin can enrol a user for dual factor authentication. To enrol the user for DFA, navigate to Configure >System > Double click the user > General Tab. Click the Enroll button. You are presented with the following message.
DFA Enrollment for User
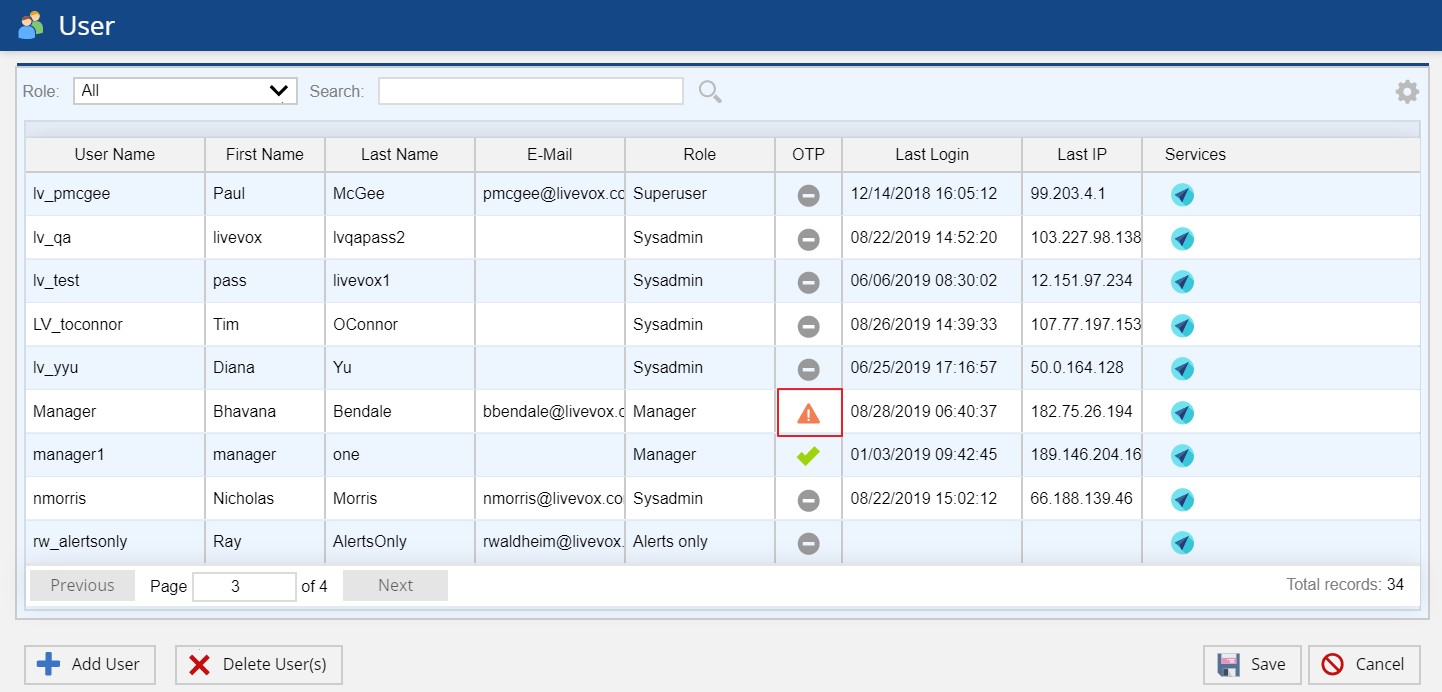
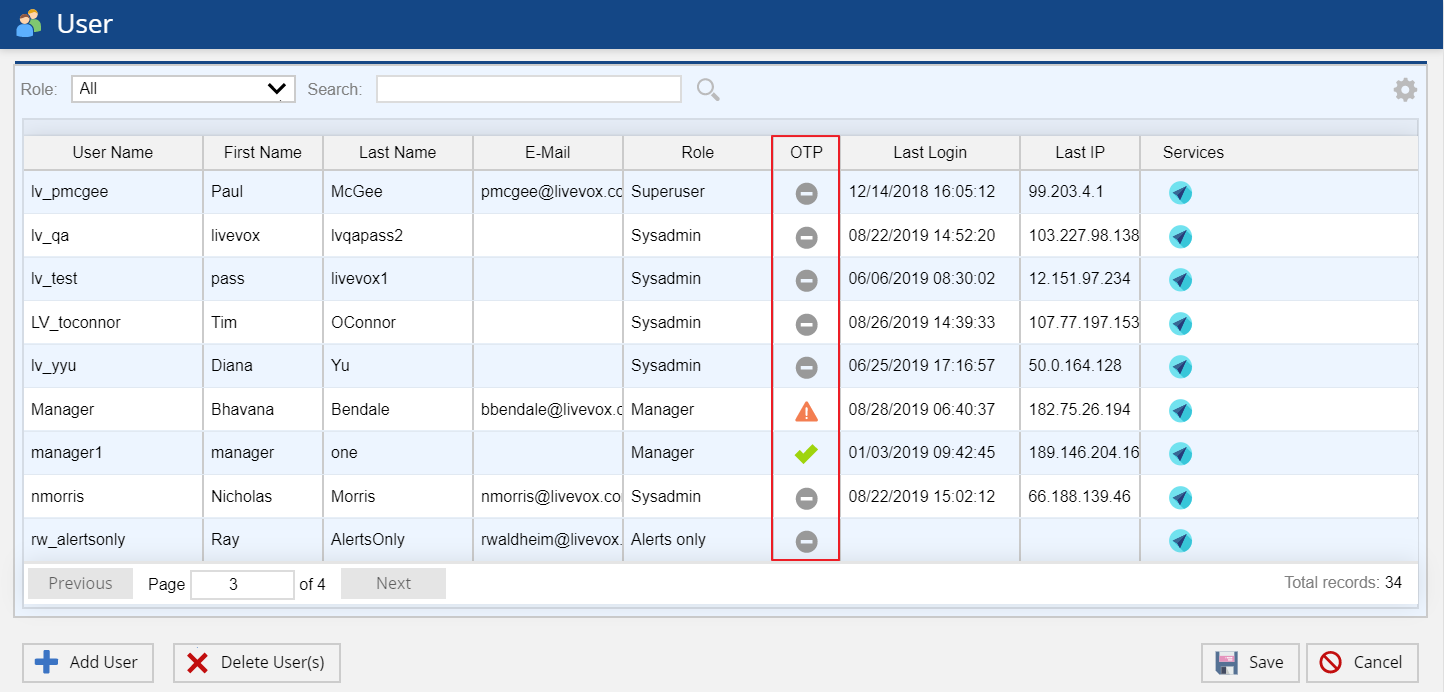
Once the enrollment option is enabled by Admin, the user’s enrollment is in pending activation status which is displayed in the OTP column of User editor.
User Account Pending Activation
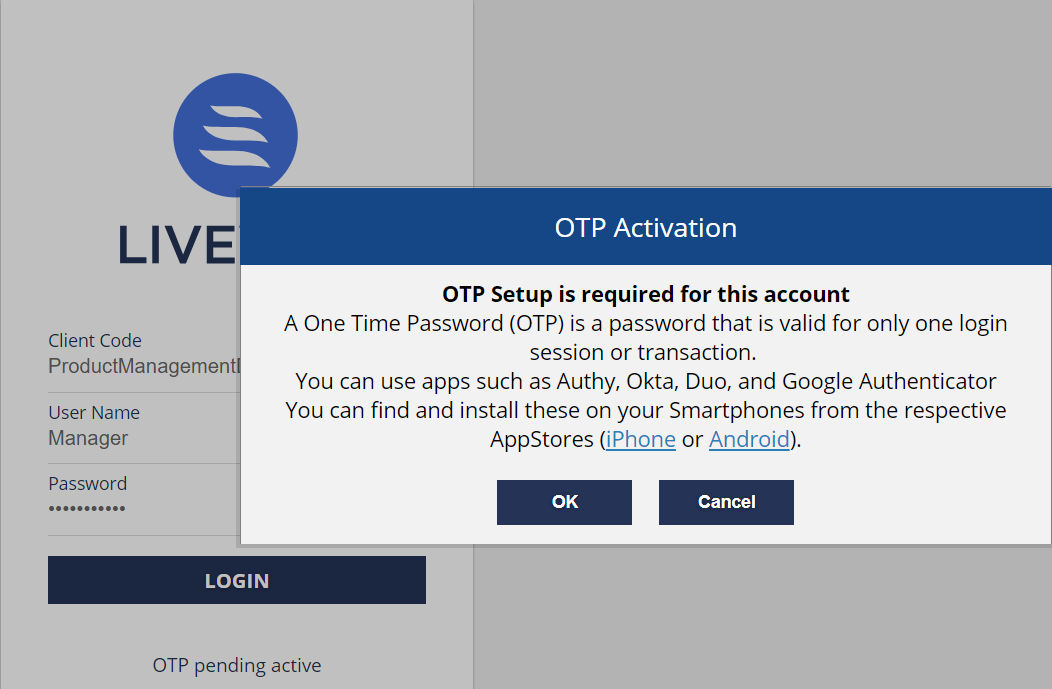
The user is required to complete this activation process upon login.
User login with Dual Factor Authentication
Users must authenticate their login with an OTP generated via Desktop Application (WinAuth), mobile application (Google Authenticator, OKTA etc.) or hardware token.
User login (User’s enrolled for DFA)
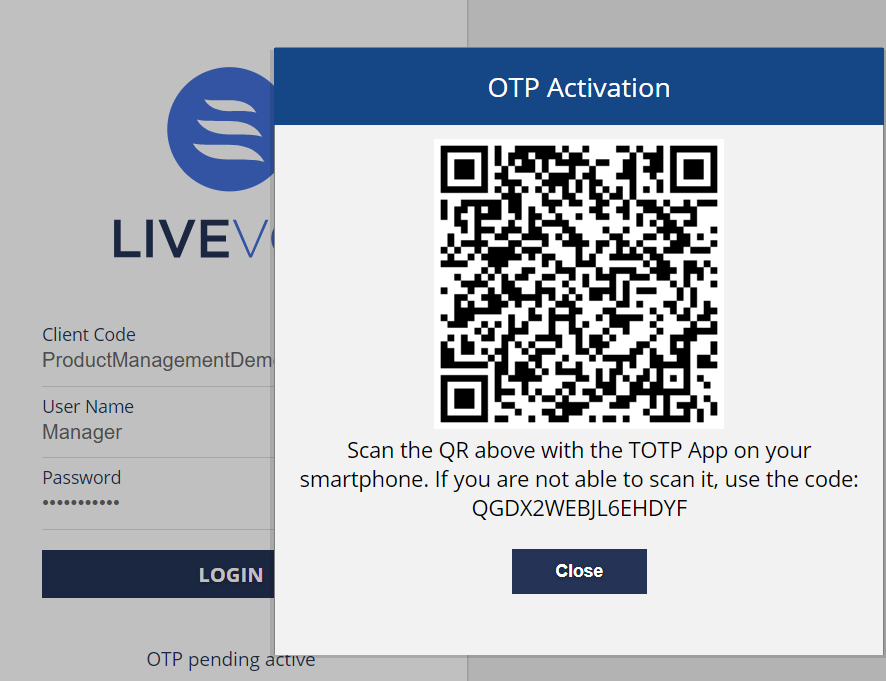
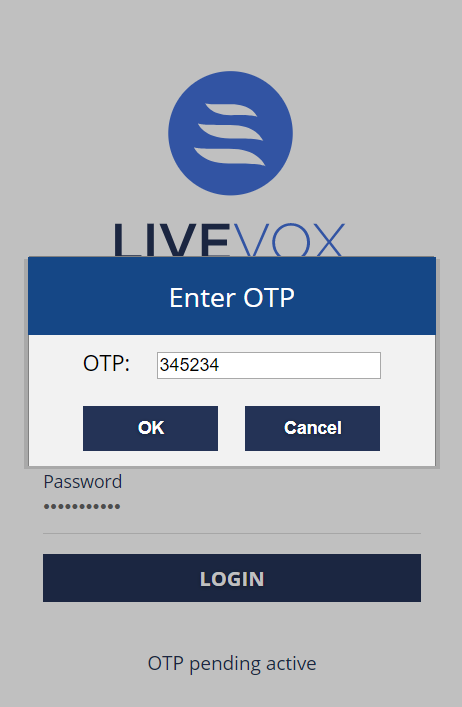
The following screen displays when the user enrolled for DFA submits the login credentials:
QR Code for OTP Activation
- Desktop Users
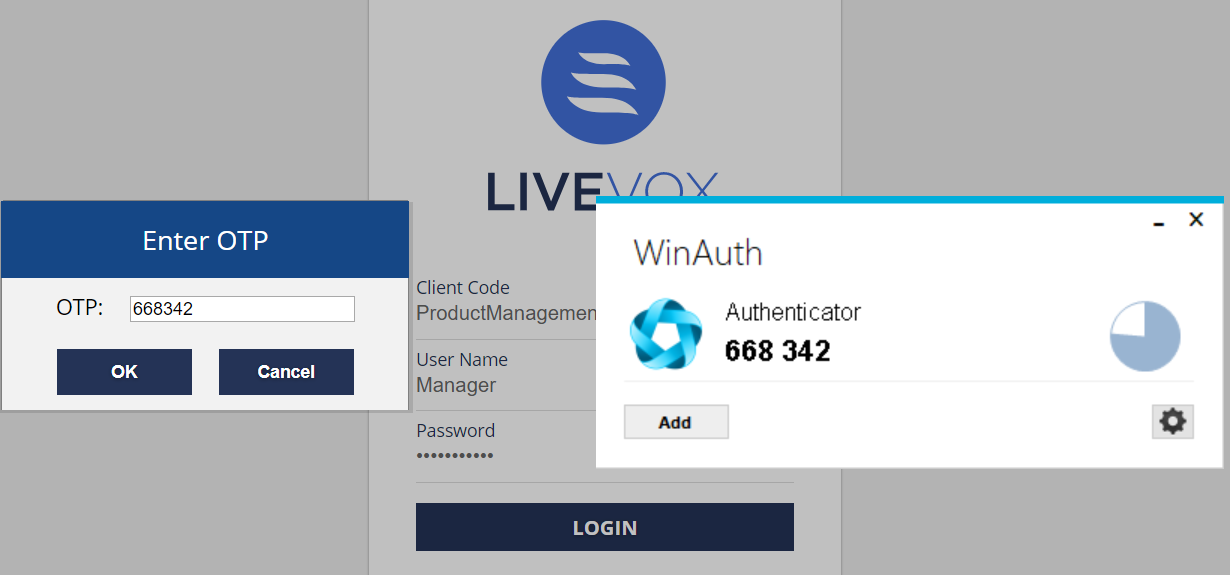
- Users are required to add the QR code in WinAuth to generate the OTP. Enter the OTP obtained via WinAuth application to continue the login process. For details on the usage of WinAuth see Setting up WinAuth Application for Dual Factor Authentication section.
OTP verification through WinAuth
- Users are required to add the QR code in WinAuth to generate the OTP. Enter the OTP obtained via WinAuth application to continue the login process. For details on the usage of WinAuth see Setting up WinAuth Application for Dual Factor Authentication section.
- Mobile Users
- Users are required to scan the QR code to continue the login process. The user receives OTP via a mobile application (Google Authenticator, OKTA etc.). Enter the OTP obtained through mobile application.
One Time Password verification - Once the OTP is entered by the user the login process continues.
- Users are required to scan the QR code to continue the login process. The user receives OTP via a mobile application (Google Authenticator, OKTA etc.). Enter the OTP obtained through mobile application.
- If there are failures, they are counted against the maximum OTP failure count and eventually the account gets locked and the user needs to contact the Admin to unlock the account.
OTP Enrolment Status
The User editor's User Grid displays a column to indicate the OTP (One Time Password) Enrolment Status. Hover the mouse over the icon displayed in the OTP column to get the description of the OTP Enrolment Status.
User editor -enrolment status
Changing Passwords
The users enrolled for Dual Factor Authentication require a valid OTP token to change the password. The login process continues upon successful validation. The OTP token validation failure is counted against the maximum OTP failure count.
Resetting Locked Accounts
The User editor displays a lock icon for a user locked due to exceeding the maximum attempts of password or OTP. To unlock the user, permitted user can double click on the lock icon and confirm the action.
Setting up WinAuth Application for Dual Factor Authentication
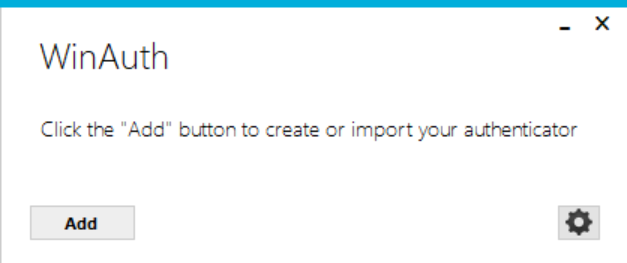
WinAuth application can be used by Desktop users to generate OTP for second level verification. Follow the below steps for initial set up of the WinAuth Authenticator.
- Download the WinAuth app by clicking https://winauth.github.io/winauth/.
- Once downloaded, double click the WinAuth application to set up a new Authenticator:
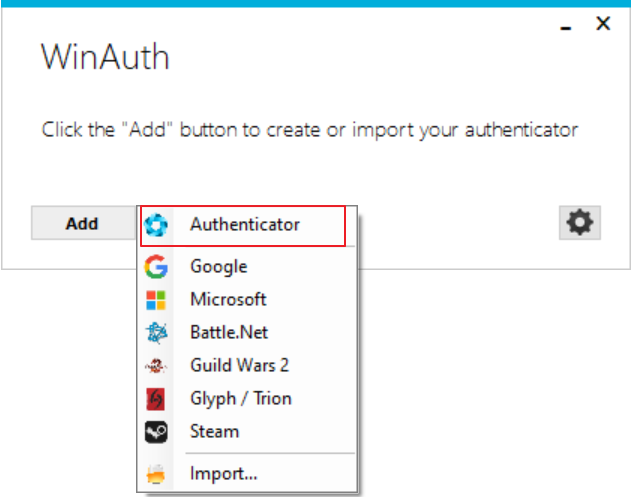
WinAuth Application - Click the Add button to set up an Authenticator.
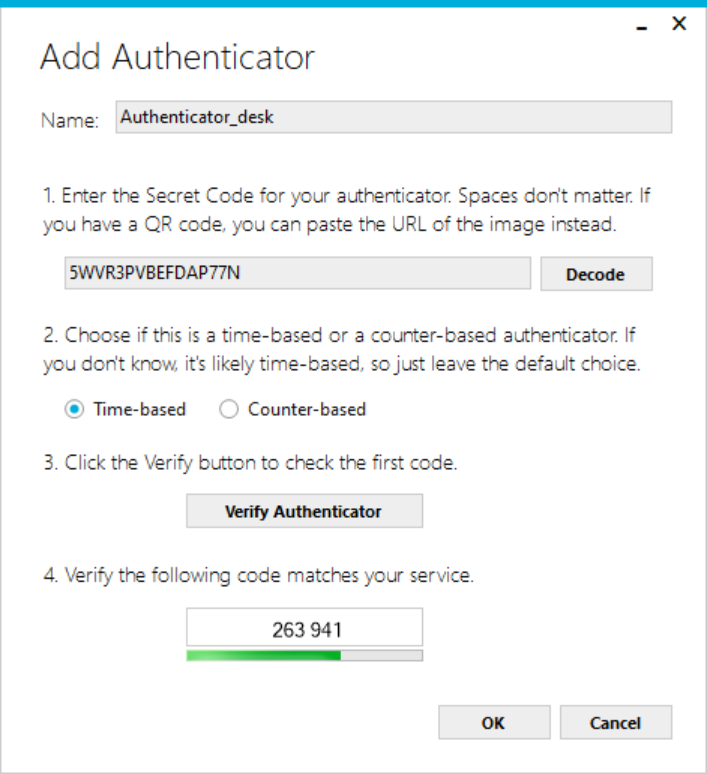
Adding a new Authenticator - You are presented with the Add Authenticator window as below.
Configuring Authenticator details
The Add Authenticator window allows you to configure the following:- Enter the name of the Authenticator in the Name field.
- Copy the QR code displayed on OTP Activation screen of LiveVox Portal into WinAuth.
- Set the authenticator type as time-based.
- Click the Verify Authenticator button in order to preview the first generated code.
- Click the Ok button in the Add Authenticator window.
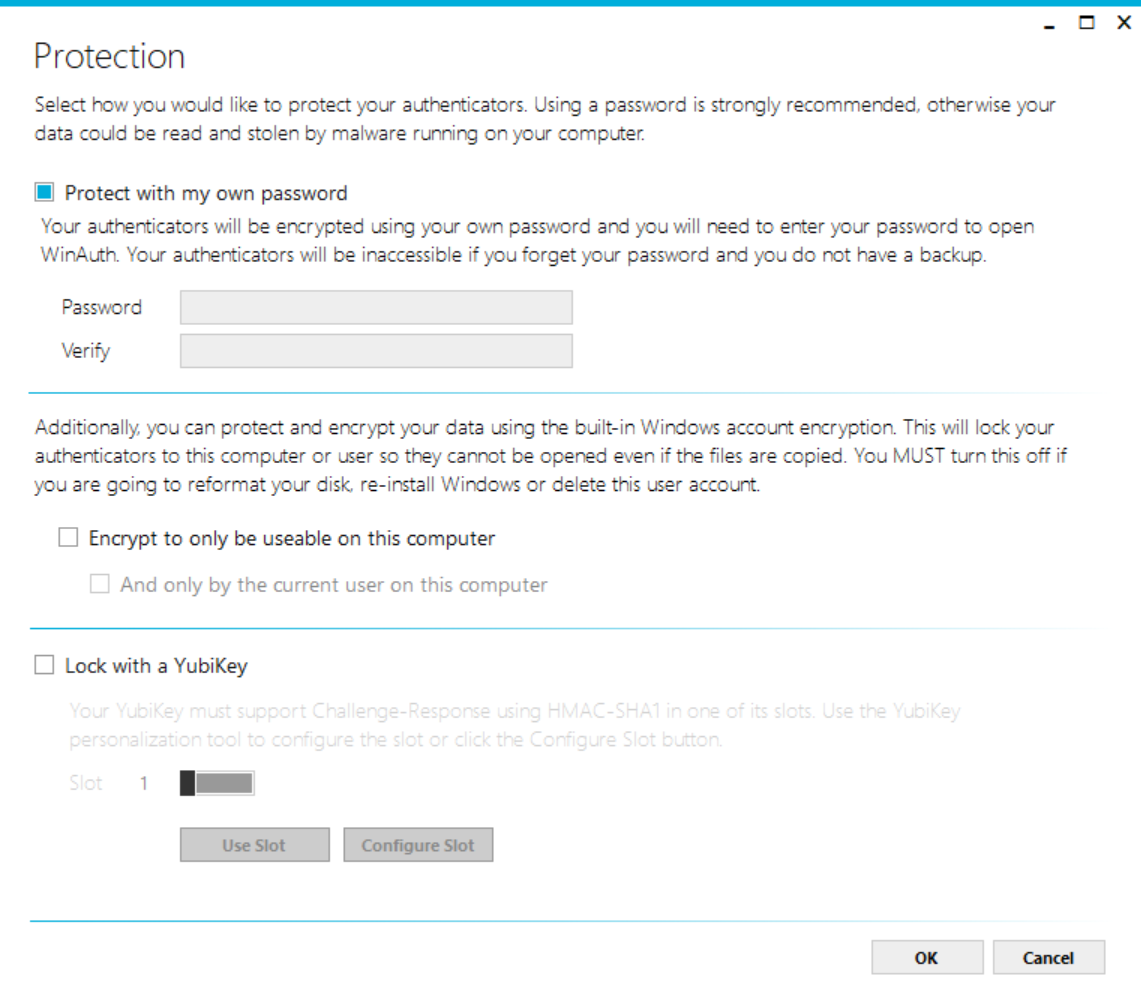
- You are presented with the below Protection screen to lock the WinAuth application, if you wish to lock the application. Set the required Password and click Ok button and use WinAuth to verify OTP as normal.
Protection config
- Close the OTP Activation window of LiveVox portal. You are prompted to enter OTP as shown in OTP verification through WinAuthscreenshot, where you can enter the code presented on the WinAuth.